A firewall is either a software-based or, in some cases, a hardware-based security system for networks. It automatically monitors traffic inflow and outflow on the system and blocks certain kinds of data flow based on rules, which are pre-configured.
In Linux, Firewalld and UFW are two of the most popular Firewall software. They are used for all kinds of traffic blocking; from blocking a certain website, to blocking a specific server.
Today we will learn how to use these two Firewalls to block a specific port in Linux.
List Open Ports in Linux
Run the following command to find open ports in Linux:
$ ss -tuln | grep LISTEN
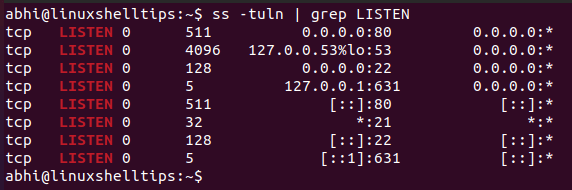
As an example, we will try to block port 22 (which is used by SSH) using both firewalls.
Block a Port Using Firewalld
Firewalld is not available in Linux distributions by default and it can be installed from official repositories.
Install it in Debian, Ubuntu, and similar distros by running:
$ sudo apt install firewalld
Install it in RedHat, Fedora, CentOS, and similar distros by running:
$ sudo yum install firewalld
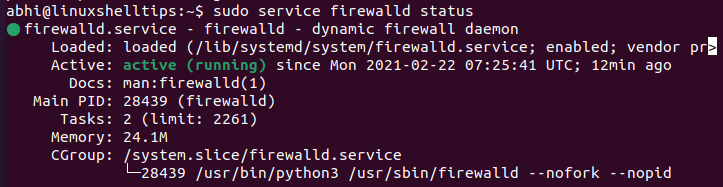
Verify if the Firewall has started by running:
$ sudo service firewalld status
Now, the syntax to block a port using Firewalld is:
$ sudo firewall-cmd --remove-port=22/tcp --permanent $ sudo firewall-cmd --remove-port=22/udp --permanent
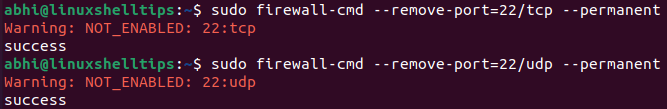
First of all, ‘firewall-cmd’ is the command for Firewalld; as Firewalld by itself runs as a background listener daemon. Secondly, 22 is the port to be blocked and ‘tcp’ and ‘udp’ are the transport level protocol to be blocked on that port. The flag ‘--permanent’ keeps the port blocked even after a restart.
Run the following for these changes to take place:
$ sudo firewall-cmd --reload
SSH is now blocked on your system and any client who tries to connect via SSH will get an error. You can enable SSH again by running the same command with the argument ‘--add-port’ instead of remove.
$ sudo firewall-cmd --add-port=22/tcp --permanent $ sudo firewall-cmd --add-port=22/udp --permanent
Block a Port Using UFW Firewall
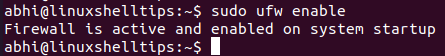
UFW stands for uncomplicated firewall and it is available by default in Linux distributions. Firstly, enable UFW with the following command:
$ sudo ufw enable
Block a port with the following command:
$ sudo ufw deny 22
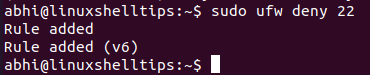
All SSH connections will be blocked now. Access to the system via SSH will result in a ‘Connection Refused’ error.
To enable SSH again, run:
$ sudo ufw allow 22
Conclusion
In this article, we learned how to block a port using two firewalls in Linux: Firewalld and UFW. There are many more options to block traffic using these firewalls; including blocking of only incoming connections but allowing ongoing connections etc.
All these options are explained in the respective man pages which can be accessed with ‘man firewall-cmd’ and ‘man ufw’. Thanks a lot for reading and let us know your thoughts in the comments below.
